On various sources on the internet I found information that the VDSL modem that I use at home is driven by a Linux system. The device is called Speedport 300 HS and is origiginally manufactured by Sphairon. For various purposes I was seeking a (serial) console access to the device. In the end I wanted to peek on the physical parameters of the (V)DSL connection and let these by documented by the dsltool plugin for fli4l routers.
During normal operation the system is not accessible on the LAN port. A serial console is of course not available directly. As I had to disassemble the device in order to change a slowly dying capacitor I analyzed the internals of the device. On the PCB there are four soldering pads that led me to the impressoin that this is possibly an access to a serial console. This assumption was later confirmed by information that I found on various sources on the internet (See [1], [2] or [3]). The only thing is that this port does not use RS-232 (±12V) levels but ±3.3V and therefore cannot be connected directly to a computers’s serial port.
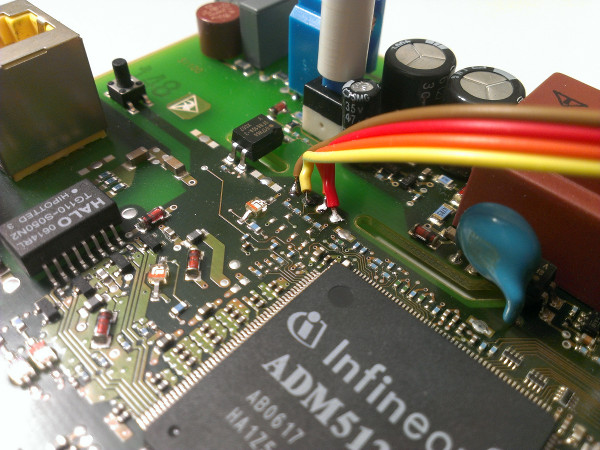
For the level shifting I acquired a simple MAX3232 circuit with a serial DB-9 connector and the external parts for the MAX µC onboard. So the rest of the work ended up in connecting the right wires. The soldering pads can be found in direct neighborhood of pin 1 of the main CPU (ADM5120P). The rightmost pin pointing to the CPU is VCC (+3.3V). The pin on the opposite is GND. These two could easily indentified with a simple multimeter. So the remaining two pins inbetween should be the RX/TX wires. These two were identified by simple try and error. Here the pin next to GND is RXD (yellow wire in the pictures) and the pin next to VCC is TXD (orange wire).
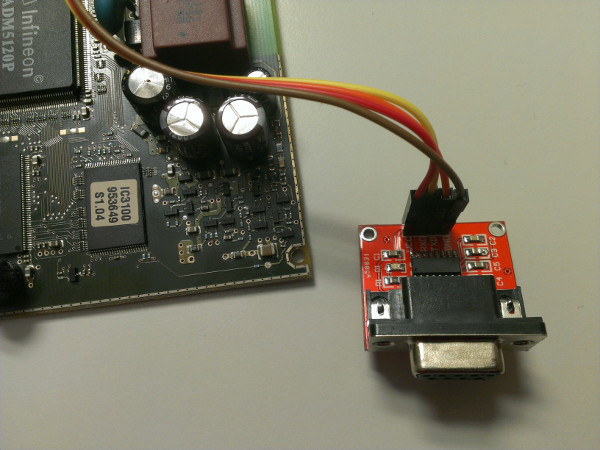
After connecting the setup to the serial port (through an USB<->RS232 adapter) and firing up the device I could see the output of the kernel during boot. The parameters for the serial console are 115,200 baud 8N1 with no hardware handshake (of course because it is a simple 3-wire-connection without RTS/CTS pins). In the end you are provided with a login. From disassembling the firmware image I know that the login is “root” and as a password set which is currently not known. John is currently working on this … ;)
Please be aware that any modification to your hardware may lead to a loss of warranty. Use this information at your own risk. I am not responsible for any damage to your equipment.
References
[1] http://www.onlinekosten.de/forum/showthread.php?t=91207
[2] http://wwerther.de/2011/04/speedport-300hs/
[3] http://www.vdsl-news.de/2007/sync-sphairon-speedport-300hs/